Overview: Security
Case Management combines comprehensive security for the LOCAL DISCOVERY database with flexibility that allows you to customize the security aspects of the product to meet your organization’s needs.
Security is established primarily with the User and Group Management features of Case Management. Security applies to functions in Review as well as Case Management and Administration. This topic explains the concepts of Case Management security and the tasks to be performed for proper management of users and groups.
Types of Security
To manage access to and changes in your LOCAL DISCOVERY data, an approach that combines user, role, and group identity with specific privileges is used. Specific types of security introduced in this topic apply to:
-
Functions that can be performed in Case Management and/or Review.
-
Access to and actions within specific cases (such as making redactions).
-
Access to and actions within specific batches (which comprise review passes).
-
Ability to view and/or change the database fields of a particular case.
Privileges Required
The privileges for managing users and groups are built into the Super and Case Administrator roles. By default, privileges for managing users and groups are as follows:
-
Super Administrators can perform all user and group management tasks. Only a Super Administrator can access the User/Group Management pages in Case Management.
-
Case Administrators can perform user and group management tasks that apply to their cases. Case Administrators manage users in the Case Management module only for their own cases. This includes assigning users and/or groups and changing roles/privileges for users/groups assigned to their cases. Case management from this perspective is explained in Overview: Edit Cases.
Before You Begin
After LOCAL DISCOVERY is installed, an administrator assigns a user's access in the Web Portal and/or in the Case Management module. In the Web Portal, when you set a user as Admin, in LOCAL DISCOVERY, the Admin is a Super Administrator who will be responsible for all user and group activities until/unless he or she defines additional Super and/or Case Administrators in Case Management or in the Web Portal. For more information, see Manage Users in the Web Portal.
For greatest efficiency, address the following issues before defining security for your organization:
Check license
Ensure that your LOCAL DISCOVERY license is sufficient for the number of users you want to add. If you have any questions about the number of seats available, contact IPRO Support.
Read/write access
Users need read/write access to the IPRO system directory. If you use alternate directories for your cases, users will need read/write access to the directories for the cases they are assigned to.
Determine password requirements
Case Management allows you to require strong passwords, which must be from 8 to 16 characters long and include at least one uppercase character and one number or special character. If strong passwords are not required, then a password that is 6 - 16 characters long is required.
|
|
Recommended: Even if strong passwords are not required, best practices call for passwords with at least one upper- and one lower-case character, both alpha and numeric characters, and at least one special character (such as ! @ # $, etc.). |
To check/change the passwords setting, see Configure System Level Options.
Plan security approach
Complete the following steps to plan your security approach:
-
Familiarize yourself with Case Management security by reading through this topic.
-
Based on the options available, evaluate roles and privileges and determine a security approach for your organization.
-
Determine which users and groups need to be added and assign their roles and privileges based on your security approach. You can add/remove users and groups at any time, as a normal part of Case Management.
Security Beyond User and Group Privileges
Privileges have meaning only if users are assigned to specific cases and/or batches (which comprise review passes). Each user, whether as an individual or as a group member, can open only those cases or batches to which he or she has been assigned.
In addition to the privileges given to an individual user or group, roles and/or specific privileges can be assigned at the case, review-pass, and/or database-field level as explained in the following paragraphs.
Case-level security
Case-level security involves defining which users will be allowed to open a case and their privileges when working in the case. See Overview: Create Cases for details.
Review-pass security
Review-pass security involves defining which users are assigned to batches, and what privileges they have while working with each batch.
Managing access to and privileges for review passes is discussed in Overview: Managing Reviews.
Database field-level security
Database field-level security also exists for cases. By default, most fields in the Case Management database can be viewed and changed by anyone assigned to a case.
As needed, the Super or Case Administrator can set individual field-level security for a case at the group or user level. Case Administrators can do so only for cases to which they are assigned. Database field-level security is discussed in Change Field-level Security.
Function-specific security
By default, individual functions in LOCAL DISCOVERY are available to users as allowed by their base security. For example, a group's right to access case reports is determined by the group’s (or individual member’s) base privileges.
At times it may be necessary to secure individual functions. For example, you want all of your users to have access to reports, but one specific report needs to be limited to the case administrator group. Access to this report can be secured in this way; this security will take precedence over other security settings.
How Does Case Management Determine Privileges?
Because privileges can be set at the user, group, case and/or review pass level, you may ask, “With so many options, just which privilege settings will be used when a user logs in and opens a case or batch?”
Case Management uses the following privilege “types,” along with the security determination flowchart shown later in this section, to determine which privileges will apply.
|
Context |
Description |
|
A role and/or specific privileges have been assigned to a user in conjunction with a specific case. |
|
|
A role and/or specific privileges have been assigned to a user in conjunction with a specific review pass (which contains the batches that users open). |
|
|
A role and/or specific privileges have been assigned to a group in conjunction with a specific case. |
|
|
A role and/or specific privileges have been assigned to a group in conjunction with a specific review pass (which contains the batches that users open). |
|
|
A role and/or specific privileges have been assigned to a user when he or she is part of a specific group. |
|
|
A role and/or specific privileges have been assigned to a group. |
|
|
A role and/or specific privileges have been assigned to a user. (These are the privileges set in the Case Management module for the individual user.) |
About the security determination flowchart
Regarding the hierarchy of questions shown in the figure, note:
-
The order of evaluation is from top to bottom. As soon as an answer is found, the evaluation stops and the corresponding privileges will be applied.
-
In this diagram, “set” means a role other than None has been selected, and privileges correspond to the chosen role or have been selected by the administrator.
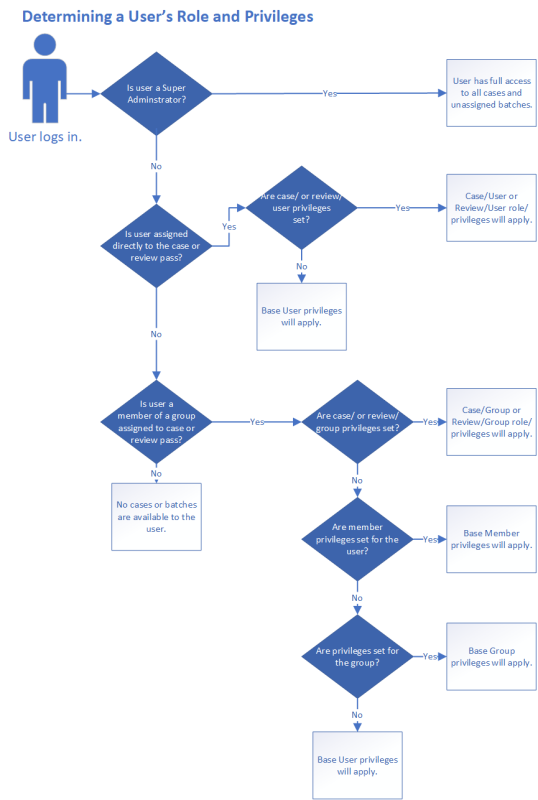
What about users with multiple role/privilege settings?
The flowchart above shows how Case Management determines which privileges to use when a user has been assigned to a case or review pass. When the user is assigned in more than one way, the following criteria are used to determine which privileges the user will have:
-
If a user is assigned directly to a case or review pass, the role/privileges set at that level will take precedence over any other settisngs.
-
If the role is set to None, the user’s base privileges will apply.
-
If the user also belongs to a group(s) assigned to the case, the group settings are ignored.
-
-
If a user is assigned to a case or review pass through more than one group (or with both group and member privileges set), all group-related privileges (member and group) are combined.
![]() Click here to view examples of how multiple assignments are treated.
Click here to view examples of how multiple assignments are treated.
Related Topics
Control System Access Using Groups, Users, Roles, and Privileges
Version: 2023.8.12
Last Revision: 11/8/2023
